Digital Identity
A framework for organizing the categories of digital identity and an analysis of where disruptive innovation is most likely to succeed.

Digitizing people’s identity to streamline their interactions with a digitally connected world is a movement full of opportunity, but also fraught with danger. While creating convenience and expanding access to services is universally desired, asymmetrical power relationships can lead to predatory practices. Whether this is a government centralizing data or a company driven by profit and expansion, the misuse of personal data is a growing cause of concern.
This concern has resulted in a movement that uses concepts like “self-sovereignty” to denote a raft of practices intended to protect individuals: data minimization, decentralization, consent, ownership, and limited access are just a few. This is a noble and timely movement, but one in which startups are challenging very powerful and wealthy incumbents. Incumbents generally are not motivated to disrupt themselves, so what strategy can effectively disrupt the entrenched digital identity market?
As Clay Christensen famously wrote 20 years ago, disruptive innovation is a process by which a new thing transforms an existing market with simplicity, convenience, and affordability where complication and high cost were the norms. This type of innovation can be hard to spot at first due to a lack of features or immediate usefulness, but it contains something new and valuable that sustains its growth over time. Just look at how portable camera phones seemed worthless at first, and then they grew to disrupt the entire camera industry.
With disruptive innovation in mind, let’s look at the digital identity problem space from a business strategy perspective. This starts by recognizing that digital identity is not one monolithic sector, but rather a collection of different categories in competition with each other. Access management, regulatory compliance, and Internet accounts are typically considered the three constitutive parts of the identity space. These sectors are where all the money is spent, where research and development are targeted, and where most public attention is focused. However, at Learning Machine, we believe there is an important fourth category: Documents. Together, these categories form an easy-to-remember acronym: ACID.
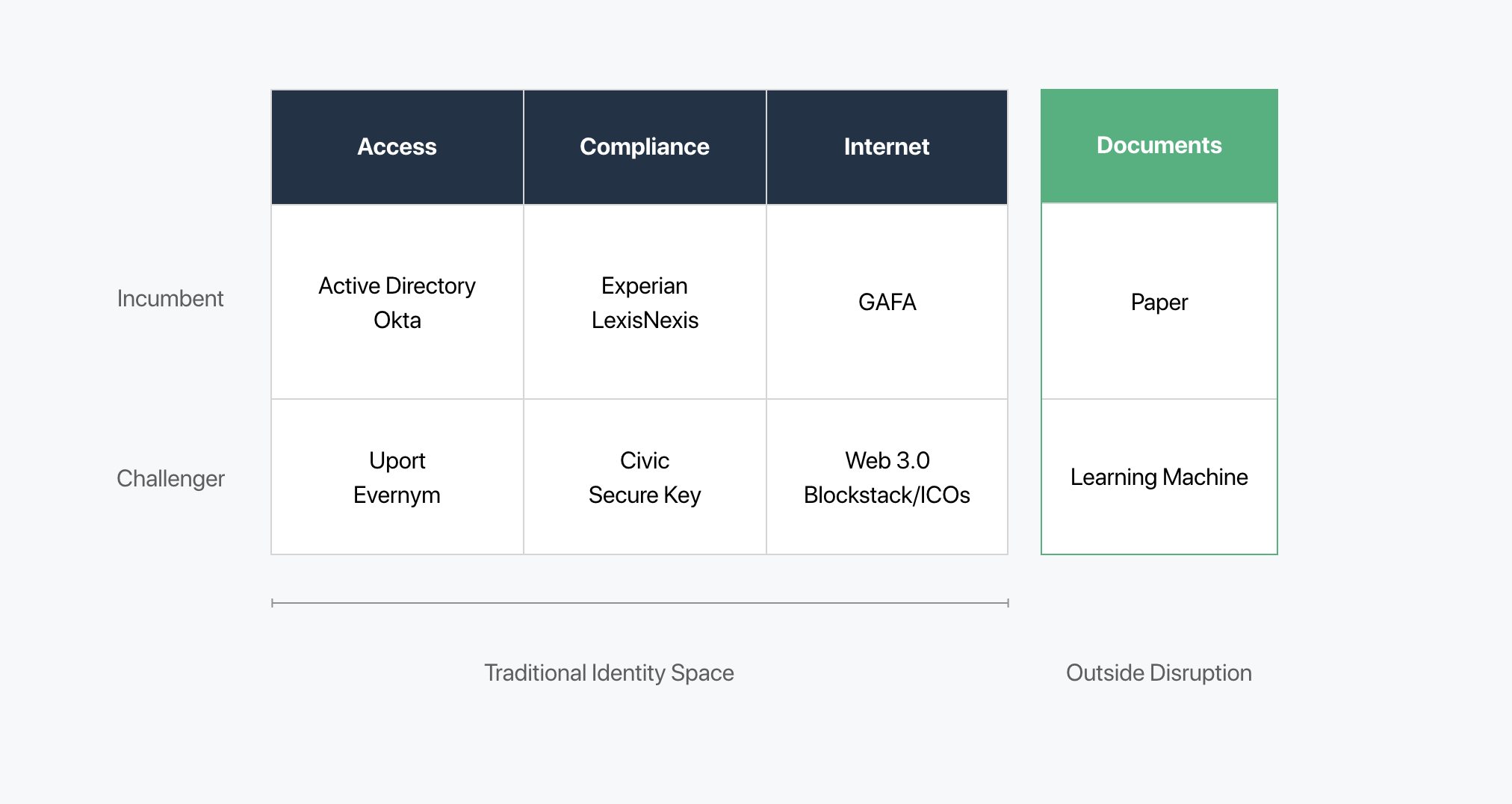
Learning Machine has made the strategic choice to disrupt paper documents with verifiable digital records (software), rather than competing directly within the traditional identity space. The following analysis explains why. Note that some startup challengers will be named as exemplars in their categories, which is not meant to imply any criticism of those companies. In fact, many of these companies are collaborating behind the scenes on data standards that will form a common foundation for future interoperability. We wish all companies fighting for self-sovereignty to have success.
Access
Access Management facilitates secure login to various ecosystems. This service is ultimately about providing login security, which necessarily creates layers of difficulty.
Examples:
- Incumbent: Microsoft Active Directory, Okta
- Challengers: Uport, Everynm
Analysis: Providing login IDs that are rooted to a blockchain and recipient-owned is an altruistic goal because it seeks to limit the leakage of personal information. However, this space already has difficulty layers in place for security, and today, managing cryptographic keys is hardly considered easy. Increasing the difficulty level and responsibility of users will make it hard to win at scale because the public generally values convenience overall. People want to be empowered, yes, but they also like having a safety net. Other well-funded technologies, like artificial intelligence, may provide better alternatives to passwords in the short term.
Compliance
Regulatory Compliance for various industries requires knowing their customer (KYC), which is part of a larger anti-money laundering (AML) initiative.
Examples:
- Incumbent: Experian, LexisNexis
- Challengers: Civic, Secure Key
Analysis: Current KYC blockchain startups are essentially just providing another vendor-controlled network. In other words, a person’s blockchain-anchored profile will only work within that vendor’s proprietary ecosystem. More importantly, these startups are relying on data that originates from incumbents like Experian, LexisNexis, and others — they are simply putting that data on a blockchain. Having a core dependency upon one’s competition doesn’t seem like a formula for effective disruption.
Internet
Identity for web-based accounts is how we use online services and social networks. Preferences are configured by people and experiences are tuned to each person’s activity history. This space has been widely covered in the news, in part due to recent violations of trust, privacy, and what many feel to be a dishonest representation of the service. While users may establish separate profiles for different services, these services gather data from beyond their walls to develop expanded profiles that are monetized in ways that violate common conceptions of privacy and trust. Due to the imbalance of power in these relationships, predatory practices often emerge where people are increasingly exploited for payment with dollars or personal data.
Examples:
- Incumbent: GAFA (Google, Amazon, Facebook, Apple, etc.)
- Challengers: Web 3.0 (Blockstack, Decentralized Apps, Tokens, etc.)
Analysis: Creating an entirely new Internet (Web 3.0) where people enter into a relationship with a service maintaining full control over their identity is an astonishingly ambitious goal formed in response to a real problem. The struggle here will be the high switching costs for regular people to move away from the traditional web, along with the vast wealth of these competitors. The extremely low number of early adopters confirms this friction. A decentralized web would be amazing, but it seems like a very long road that will be strewn with startup casualties along the way. ICOs and tokens are interesting because they have created a new funding mechanism to extend the runway for many of these initiatives, but that doesn’t change the uphill dynamics.
Documents
Official documents (paper) still run the world. Processes like certification, testing, inspection, health, employment, finance, personal ID, and education still create paper trails to elicit trust and rely on postage to send these trusted artifacts. Just look at how the Apostille Process (notarization) is still the de facto standard for international law. Even PDFs are essentially just paper equivalents with most of the same limitations.
Today, these documents are relatively easy to fake and difficult to transmit or verify. And yet, official records are potentially a powerful form of social currency because they allow people to authentically represent their various achievements, experiences, and characteristics (aka attestations or verifiable claims).
Examples:
- Incumbents: Paper, wax, postage
- Challengers: Learning Machine
Analysis: We believe that replacing physical credentials (documents) with programmable ones (software) is the most effective way for a startup to disrupt the identity space. The processes surrounding paper to make it certified isn’t convenient and paper inherently lacks powerful features like self-attestation and built-in machine readable data. Further, public blockchains provide a global verification network that can ensure the integrity, ownership, and authenticity of these new digital records. Of course there are other digital approaches to the document space, like Adobe’s Document Cloud/Blue Ribbon. Their pre-blockchain approach has wide adoption and is a precursor to documents as software.
Replacing a centuries-old technology with a natively digital object has dramatically more value for issuers, recipients, and verifiers, making this a winnable category in the short term and potentially disruptive to the entire identity space long term. This approach is easy to adopt and the Learning Machine Issuing System is currently being rolled out across entire countries. That’s innovative disruption.
Summary
When we examine the various parts of the digital identity sector, we have to ask where smaller companies can most likely make an impact. Historically, this doesn’t happen by going toe-to-toe with established incumbents. Rather, innovative disruption happens by developing something that has 10x value, a process that typically must start outside the mainstream.
One way disruption gains traction is when it surfs a secular trend with powerful momentum. In the case of digital identity, public decentralized blockchains are providing that momentum and the most successful approaches will be fully aligned with that power.
From our point view, competing in the traditional identity space with a blockchain solution offers little added value today and is sometimes at odds with the underlying values of public blockchains—decentralization, permissionless innovation, and inclusiveness. For instance, KYC is necessarily centralized, hierarchical and exclusionary, which makes using a blockchain an unusual tool of choice.
On the other hand, replacing documents with software has clear 10x advantages that empower individuals with social currency for a lifetime. This approach is full of winnable markets and completely aligned with the values of decentralization, greatly increasing the effectiveness of these records as well as the transformative potential for this strategy.